Cyber Security MS
Latest News

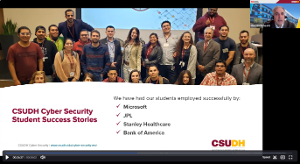
The award-winning Master of Science in Cyber Security Degree Program prepares students for professional careers in cyber security.
The program was developed and is hosted by the CSUDH Computer Science Department. Students develop the technical skills to protect IT infrastructures, operating systems and networks from intentional and unintentional informational security breaches, as well as advanced expertise in the areas of cyber security, including the protection of computers, networks and programs from unauthorized access, alteration or damage of data.
The program is designed to provide students with up-to-date specialized and advanced knowledge, while developing analytical and practical skills necessary to stay abreast in the ever-changing field of cyber security. The program benefits both traditional students as well as working adults seeking advanced degrees in their professions or in new careers. The curriculum, delivered in an accelerated 18-month cohort model, requires completion of six (6) core and four (4) elective courses. The program culminates with a cyber security research project supervised by a faculty member.
Don't have a background in computer technology? Take our Cyber Security Certificate of Completion. If you meet all other admission requirements, these 3 courses will get you up to speed to participate in the MS Cyber Security program.
Program Features
- Well-balanced curriculum combining theory and hands-on activities
- Accelerated, 18-month cohort model
- Friday evening, Saturday and Sunday classes for working adults
- Affordability
- Provides up-to-date knowledge, and the skills necessary to stay current with the ever-changing field of cyber security
Learning Outcomes
Students graduating with the CSUDH MS Cyber Security degree will be able to:
- Identify components of an information security policy including ethical considerations and explain the related research analysis
- Acquire in-depth comprehension of Informational Assurance (IA) to ensure confidentiality, possession control
- Conduct and evaluate forensics investigations pertaining to monitoring and analyzing computer network traffic via local and WAN/Internet
- Produce a cyber security system that detects, monitors, and mitigates cyber
- Distinguish methods of defense fortification and identify levels of
- Apply principles of access control models and techniques to create authentication in advanced communication system
- Evaluate security aspects in Cloud
Employment Opportunities
According to the U.S. Bureau of Labor Statistics, employment of information security analysts is projected to grow 18 percent from 2014 to 2024. Rapid growth of the information technology sector, as well as the use of information technology in every professional field, has led to ever-increasing demands for specialists in the field of cyber security.
View our most recent webinar:
View recordings from ToroHack 6.0:
https://csudh.techsmithrelay.com/collections/g018500PvXhE3xhYEnJwgWXMWfpr7